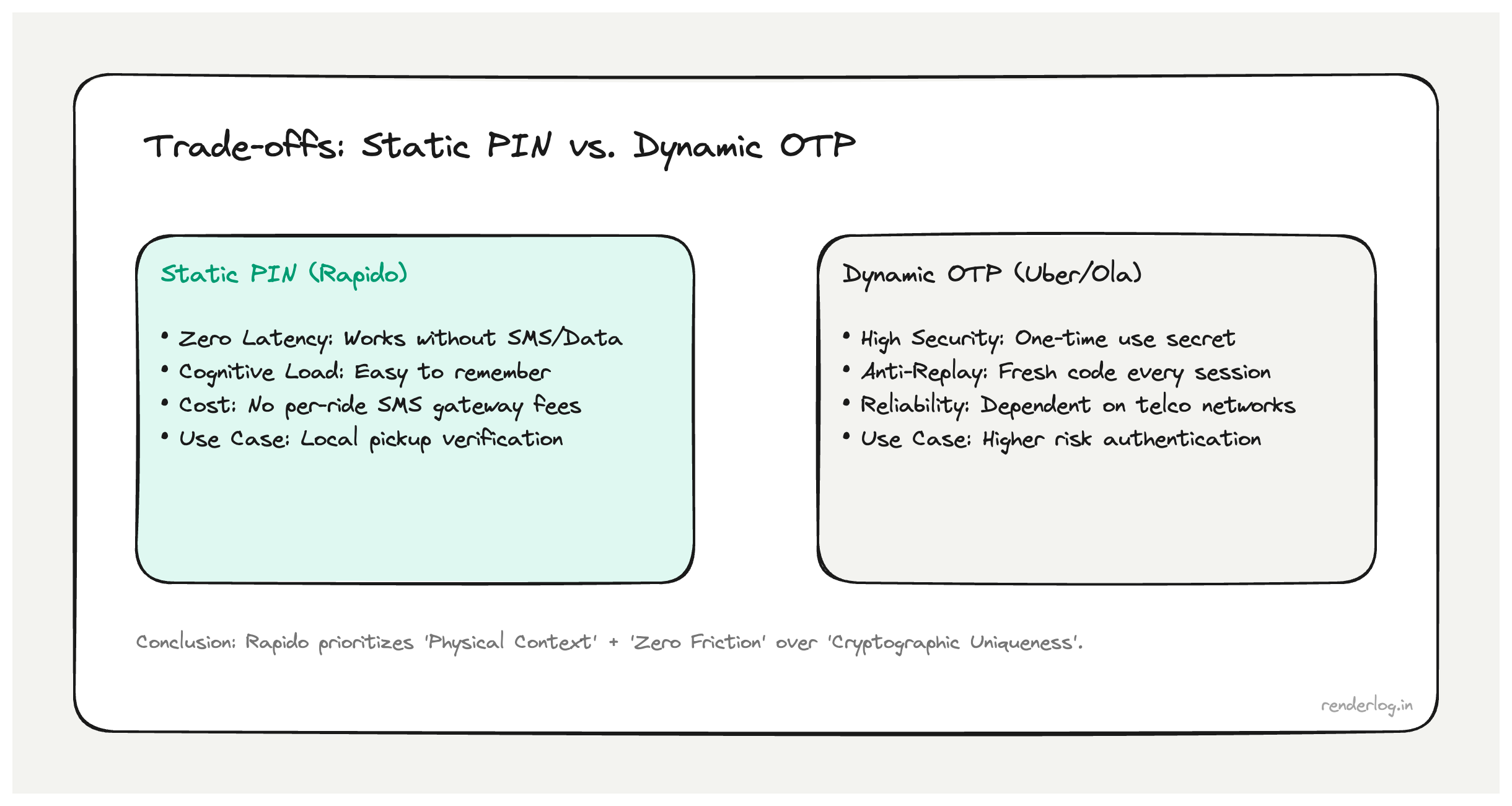
If you use Rapido, you may have noticed the same four-digit Rapid PIN on ride after ride. Uber and Ola often lean on fresh SMS codes; Rapido leans on a stable number. The first engineering reflex is security discomfort: a static OTP sounds like a bug. In product terms it is usually a deliberate trade: availability and speed over per-ride cryptographic freshness, with a threat model built around physical pickup, not remote account takeover.
This post breaks down why that design can make sense: friction, cost, verification vs authentication, and when “best practice” (dynamic OTP) is not the best fit.
Friction at the kerb
Ride-hail in dense Indian cities is often urgent: low battery, patchy data, one hand on luggage, captain already at the corner. Waiting for SMS, parsing a new code, or digging through notifications costs real seconds at the kerb, not just server milliseconds.
A memorized fixed PIN lets riders confirm start when they see the right vehicle, even if SMS is delayed or data drops. That is UX engineering: optimize for a successful handshake at pickup, not for OTP hygiene alone.
Cost and backend load
Dynamic OTP flows imply, for every booking (or many state transitions):
- Generate a secret, store it with TTL, enforce replay rules.
- Call an SMS gatewayper-message pricing, vendor latency, delivery failures.
- Handle retries, timeouts, and support load.
A static PIN tied to the account removes per-ride SMS from the critical path in many implementations and shrinks moving parts in the booking state machine. At high ride volume, SMS margin is not rounding error.
Exact internals are proprietary; the economic shape is familiar to anyone who has operated OTP at scale.
Threat model: verification, not fortress auth
Ten thousand four-digit combinations is weak entropy against offline brute force. That math misses the attack you are usually defending:
| Goal | What a static PIN is good at | What it is not trying to be |
|---|---|---|
| Wrong pickup / fake start | Fast shared secret between rider and captain | Remote login barrier |
| Driver-side mix-ups at handover | Simple checkpoint at the vehicle | Bank-grade MFA) |
To abuse this model, someone typically needs the PIN and physical alignment with your pickup window and assigned vehicle contextoperations, GPS, and fleet logic add layers beyond the digits alone.
That does not make static PINs right for every productit means Rapido-style flows optimize for verified handoff, not internet-scale proof of identity.)
When dynamic OTP is still best practice
Fresh secrets matter when the channel is remote (banking, high-value fraud), replay breaks your business rules, or regulators require step-up auth. Rapido’s pattern is closer to “prove you are the person at this spot right now” than “prove you control this account from anywhere.” Different job; different tool.
Takeaway
Static Rapid PINs are less about pretending four digits are unbreakable and more about zero-friction verification, lower SMS and server churn, and security that matches how rides actually start. Solid systems design names the threat model, the user moment, and the cost linethen picks the simplest control that still winsnot whichever pattern topped a generic checklist last quarter.